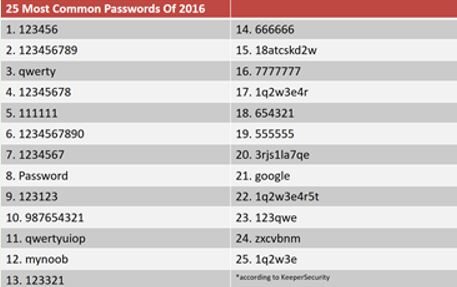
Passwords Are Terrible Protection
For most of us, nearly all the "stuff" we have access to online - I'm talking about years' worth of emails, our company's servers, files on cloud services, online shopping accounts - is protected by a username/password combination, probably a poor one if statistics are any indication. I’ve shared in previous articles some of the big problems with passwords, namely the human factor. To make them easier to remember, we typically choose passwords that are trivial for computer password-cracking algorithms to guess. This is bad enough. But it gets worse.
 Even if we are among the minority who use “good” hard-to-crack passwords, we often use the same password across many accounts. That means if a hacker gains access to a password list from one site, say a breach at Twitter, now they have a “key” (email/password combo) that they can try in many different “doors” (i.e. other sites like Google, Amazon, Facebook) to see what they can unlock with it.
Even if we are among the minority who use “good” hard-to-crack passwords, we often use the same password across many accounts. That means if a hacker gains access to a password list from one site, say a breach at Twitter, now they have a “key” (email/password combo) that they can try in many different “doors” (i.e. other sites like Google, Amazon, Facebook) to see what they can unlock with it.
So-called “black hat” hackers with access to your password, now can access everything in your account, plus any other accounts where you might have used the same password. Not only that, but they can essentially pretend they’re you, and start doing things as “you” like online shopping, sending emails to your contacts, etc.
Poor Password Leads to Fraudulent Email with Many $$$ at Risk
Very recently, we had a situation where a user at a business we work with had his password compromised. The bad guy jumped in on a real email conversation, pretending to be this employee, and sent an email instructing someone involved in an actual transaction with this company, instructions to wire money into a fraudulent bank account. I had previously seen examples of spoofed emails like that, but this was the first time I saw one that used the actual credentials of the user. In that sense, it wasn't a "fake" because as far as any of the email servers knew, it was actually this person sending his own email from his own account. There was no way to tell the difference, except when we dug into the logs, we saw that the email message got sent from an IP address located in Dubai, rather than here in Illinois.
This is a HUGE problem, and this kind of attack is getting more prevalent. It only takes one mistaken wire transfer of a few hundred thousand dollars to make it well worth the attacker’s effort. And, needless to say, that kind of financial loss could wipe out a business or individual. And you thought Ransomware was bad…
What is Multi-Factor Authentication?
MFA would have helped in that situation by requiring the bad guy to prove he is the user in question, with more than just a password. The idea behind MFA is that your username/password combo is only one of several “factors” needed to prove that you are who you say you are.
 With MFA, you need something more -- a second factor -- in order to be granted access. Often that is a text message containing a short code to be typed in. The idea there is to prove you not only have the user's password, but you have the user's phone too, making it more likely that you are really the person you say you are.
With MFA, you need something more -- a second factor -- in order to be granted access. Often that is a text message containing a short code to be typed in. The idea there is to prove you not only have the user's password, but you have the user's phone too, making it more likely that you are really the person you say you are.
Other examples of MFA that you may be familiar with include fingerprints or face recognition, small fobs that generate "one time passwords" in addition to the regular password, confirmation emails, and phone calls, similar to the text messages mentioned above. You may hear MFA referred to as "something you know (password) plus something you have (phone/fob), or something you are (fingerprint or facial recognition)." A growing method is the Authenticator App, which I’ll write more about next time.
Put MFA in Your Technology Plan for 2019
As you make plans for 2019, if you aren’t thinking about enabling Multi-Factor Authentication at your business, we would strongly encourage you to give it serious consideration. There will always be someone who will complain or resist any change, that’s to be expected. But there’s too much at stake to ignore this simple security improvement.
Using Conditional Access rules, you can minimize the inconvenience by only having the system prompt for a 2nd factor when the access is coming from outside your office, or from an unfamiliar device, for example. If you’re an Office 365 user, Microsoft has a lot of options for improving security, including MFA, as part of Enterprise Mobility + Security licenses that can be added to your subscription. They are even rolling out a form of MFA that doesn’t require you to type in your password at all! Curious about how that works? So was I, so I’ve been testing it. I’ll give a full report next time, so stay tuned!
 Dan Bremner, President, Castema Technology Services, Inc.
Dan Bremner, President, Castema Technology Services, Inc.


You must be logged in to post a comment.